Password & Hash Cracking Basic Commands
Hashcat
/etc/shadow hashes
https://samsclass.info/123/proj10/p12-hashcat.htm
hashcat -m 1000 hash14.txt /usr/share/wordlists/rockyou.txt --show
hashcat -m 1000 hash14.txt /usr/share/wordlists/rockyou.txt -r /usr/share/hashcat/rules/best64.rule --force
hashcat -m 1000 hash14.txt /usr/share/wordlists/rockyou.txt -r /usr/share/hashcat/rules/best64.rule --force --show
NTLM hashes
hashcat -m 1000 -a 0 hashes.txt [path/to/wordlist.txt] -o cracked.txt
MySQL 4.1
hashcat -m 300 hash.txt /usr/share/wordlists/rockyou.txt
John
john --format=sha512crypt --wordlist=/usr/share/wordlists/rockyou.txt hash.txt
john --wordlist=[path/to/wordlist.txt] hashes.txt
Unlikely to see yescrypt as an actual attack vector but keep it in the toolbox, hashcat doesn't have a code for this yet.
john --format=yescrypt hash.txt --wordlist=rockyou.txt
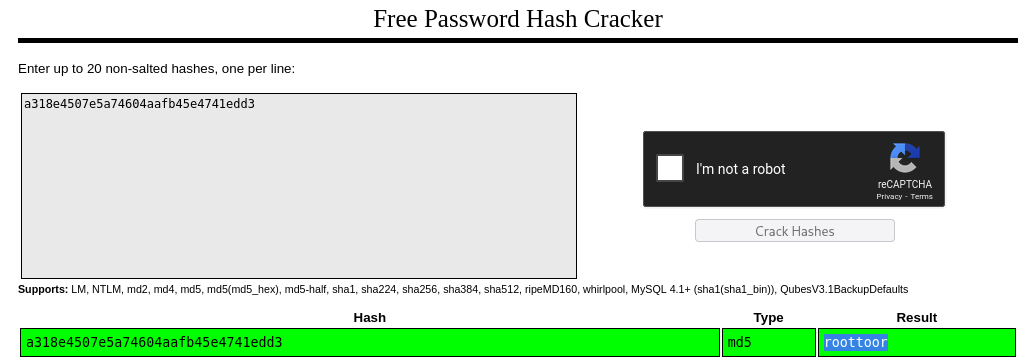
Crackstation
Some MD5 hashes won't crack with john or hashcat. Try this as a last resort.
https://crackstation.net/
Kerberoasting - Crack SPN Hashes via exported .kirbi tickets
- Walkthrough: https://www.ired.team/offensive-security-experiments/active-directory-kerberos-abuse/t1208-kerberoasting
Locally crack hashes
python3 tgsrepcrack.py rockyou.txt [ticket.kirbi]
Crack hashes on target
Invoke-Kerberoast.ps1
Use JohnTheRipper to crack SPN hashes
python3 kirbi2john.py -o johncrackfile ticket.kirbi
john --wordlist=rockyou.txt johncrackfile